Introduction and age concerns
If you are reading this then
Whether you have a keen interest in technology or work as a developer, programmer, support professional, administrator or IT manager, you'll likely find these dark secrets fascinating reading...
Why is a lot of software so buggy?
When you have updated the software on your smartphone for the umpteenth time due to "bug fixes and performance improvements" you may wonder why so many updates are needed.
The truth is that most software developers aren't all that good at their job, writing code that is simply not fit for purpose. This leads to bugs, flaws and spiralling costs of developments. We all need software to function in our daily (civilised) life so there is a big demand for programmers that outstrips the number of actual decent developers, leading to the situation we have at present.
But also, fixing bugs is an expensive process, and at some point the money runs out and code has to be released in order to get some revenue back from it. Automated testing can help but this may only reduce failure rates down to about 40%.
Don't get old
We can't stop aging but it appears we also can't stop being discriminated against because of age. The older people get, the more likely they are to find getting a role in IT a hard job in itself.
Technology is obsessed with looking young and being hip and trendy. In the US, according to statistics from the Bureau of Labor Statistics and Census, while salaries increase for engineers in the semiconductor sector in their 30s, this slowed after the age of 40 and actually fell for those in their 50s.
Another survey carried out by recruitment consultants Greythorn found that nearly three quarters of IT professionals thought the industry discriminated against older workers.
Ros Altmann, the government's tsar for older workers, told the $4 that workers with the old 'O' levels were suffering rejection from jobs, and were at a disadvantage in the job market.
When old IT equipment goes missing
Old computers never die, they get repurposed by your
It may seem like a victimless crime, but more often than not, computer equipment contains sensitive data that an organisation may not want leaving the infrastructure. Many organisations still haven't got processes in place to make sure that any device leaving the network permanently has data wiped off it completely.
Insider threats and qualification quirks
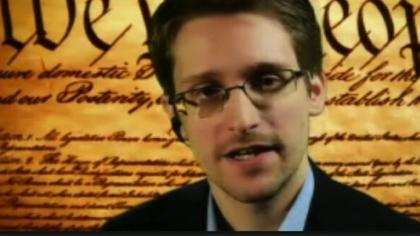
Does your firm have a Snowden ?
With the $4 still fresh in the minds of many, we know just how much damage a disgruntled employee can wreak if given the impetus to do so.
In fact, it is very easy for anyone in IT to sift through all the data coming in and out of an organisation's network should they be minded to do so. The enterprise can only be as secure as the ethics IT administrators live by. Administrators are privy to far more data than they need to be to carry out their role - and, to be honest, the same argument can be made about the humble user.
The common "insider threat" problem means that organisations should operate on a "least privilege" model that means people have access to the minimal amount of data possible, and that data access is continually monitored.
Consultants taking the credit, and dodging blame
From time to time, consultants can be brought in to help implement particular systems. When it all works, it's great but some consultants will try to take all the credit for the implementation.
Equally, if things go wrong with a project, these consultants can put the blame on IT staff and argue that the system works elsewhere, and the problem lies in how local IT infrastructure is implemented.
IT certifications don't mean a person is good at their job
Recruiters and human resources personnel use certifications as a way of trawling through the hundreds of job applications they get when sourcing personnel for roles within the IT organisation. It's a quick fix that matches up people to roles. But old-timers will often lament that people hired on the basis of how many certificates they've got may not have the real world experience to actually do their jobs.
While a certificate may get someone through the door and show that they are dedicated to a career in IT, it is not that great a gauge that the person is any good at their job.
There is no perimeter in IT security
With infrastructure there is often talk about guarding the perimeter from hackers. The truth is, there is no perimeter and believing there is one is like believing in the Easter Bunny.
And if there was a perimeter, where would it be? Organisations and security vendors can't really define where the perimeter is. It could be the endpoint, the user or where the physical network actually ends. Putting controls on any of these will give an organisation a false sense of security as hackers could simply find another way in.
And if anything, the cloud makes this worse with applications and servers running outside of the traditional network, but still interacting with users within that network as well as those outside it.
It is better to design security with no assumption of a perimeter - for example, guarding a firm's data is a better bet for security.