- Home
- Enterprise
- Mobile
- Here's what we know about the secretive company building terrifying tools to hack your iPhone
Here's what we know about the secretive company building terrifying tools to hack your iPhone
NSO Group was founded in late 2009 by serial entrepreneurs with ties to the Israeli government.

It's hard to figure out what the company actually does.
The company describes itself in vague terms on its LinkedIn, saying it is "a unique company in the field of Internet security software solutions and security research. It is responsible for many unique developments on both mobile and PC environments. The company also specializes in creating highly sought solutions in the mobile and PC controlled environments."
Though that description offers little of substance, the profile's listed specialties of internet security, mobile security, cyber threats, and penetration testing give a better idea of the high-tech spying tools it develops.
NSO currently employs more than 120 people, according to its numbers on LinkedIn. That's more than double the head count it had two years ago.
But clearly, the company's specialty is the field of 'cyber warfare.'

A brochure uploaded online by Privacy International from the company gives more insight into what it really does, which is to offer mobile hacking solutions for a variety of phones exclusively for the use of governments, law enforcement, and intelligence agencies.
NSO Group says it is "a leader in the field of cyber warfare" that utilizes its proprietary monitoring tool it calls "Pegasus," which can monitor and extract all data from a target "via untraceable commands" which allow "remote and stealth."
Its software is purchased by governments all over the world for millions of dollars.

Its clients have reportedly included Panama and Mexico, though a person familiar with the company told the Wall Street Journal it does business all over the world.
NSO received $8 million from Panama's government for its Pegasus spy software, according to a local press account. And with this latest research from Citizen Lab documenting an attack on Ahmed Mansoor, a human rights activist living in the United Arab Emirates, it's likely that government has purchased the software as well.
NSO's 'Pegasus' spy tool transforms a variety of phones into mobile listening stations.

NSO showed off demonstrations of its mobile phone hacks on a BlackBerry, iPhone, and Android phone in 2013, according to leaked emails from a breach of Hacking Team, a competitor of the company based in Italy.
"Your smartphone today is the new walkie-talkie," NSO cofounder Omri Lavie told the Financial Times that year. "Most of your typical solutions for interception are inadequate, so a new tool had to be built."
Pegasus can infect a targeted phone in two ways, both of which are through SMS text messaging. Its "zero-click" vector allows an attacker to send a special SMS message to a target which causes the phone to automatically load a malicious link, while its "one-click" vector requires a user to click a link to infect their device, which happens in the background without a user ever knowing.
Once infected, spies can actively record with the phone's microphone or video camera, grab personal data like calendars, contacts, and passwords, or download all the data on the device, to include emails, photos, and browsing history.
"We’re a complete ghost," Lavie told Defense News in 2013. "We’re totally transparent to the target, and we leave no traces."
Pegasus used a sophisticated method for hacking into the latest iPhone software.

In order to attack the latest iOS software, the company's spyware utilized three "zero-day" exploits — which are bugs that have not yet been fixed — which Lookout called "the most sophisticated attack" it had ever seen.
Lookout believes Pegasus has possibly been in use to hack iPhones going all the way back to iOS 7. Apple's latest software update, iOS 9.3.5 (which was released Thursday), prevents this attack from working.
NSO doesn't even have a website.
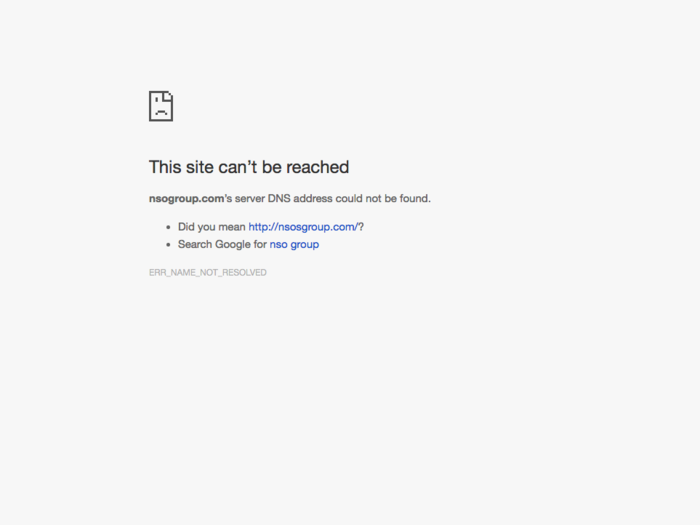
NSO Group does have a LinkedIn profile which lists nsogroup.com as its domain name, but that, unfortunately, leads to nowhere. A look back at their website through history via The Wayback Machine showed four different snapshots taken, all of which were just placeholder pages.
Though the domain name was registered in April 2008, it doesn't seem to have ever had any content for potential customers to view.
Popular Right Now
Advertisement