- Home
- slideshows
- miscellaneous
- The 21 biggest data breaches of 2018
The 21 biggest data breaches of 2018
21. British Airways — 380,000

20. Orbitz — 880,000
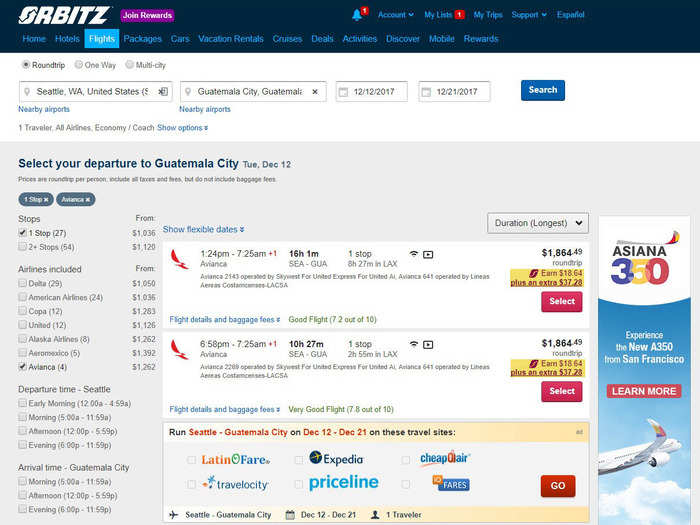
What was affected: Payment card information and personal data such as billing addresses, phone numbers, and emails.
When it happened: January 1, 2016 — December 22, 2017
How it happened: Hackers accessed travel bookings in the website's system.
Source: Reuters
19. SingHealth — 1.5 million

What was affected: Names and addresses in the Singapore government's health database, and some patients' history of dispensed medicines. Information on the prime minister of Singapore was specifically targeted.
When it happened: May 1, 2015 — July 4, 2018
How it happened: Hackers orchestrated a "deliberate, targeted, and well-planned" attack, according to a statement.
Source: BBC
18. T-Mobile — about 2 million

What was affected: Encrypted passwords and personal data, including account numbers, billing information, and email addresses.
When it happened: August 20, 2018
How it happened: An "international group" of hackers accessed T-Mobile servers through an API.
Source: Motherboard
17. myPersonality — 4 million

What was affected: Personal data via Facebook customers who used the myPersonality app.
When it happened: The app was "mostly active before 2012," but was banned from Facebook this year in April.
How it happened: The app mishandled Facebook user data by sharing "information with researchers as well as companies with only limited protections in place."
Source: Business Insider
16. Saks and Lord & Taylor — 5 million

What was affected: Payment card numbers
When it happened: Details were never shared.
How it happened: "New York-based security firm Gemini Advisory LLC says that a hacking group called JokerStash announced last week that it had put up for sale more than 5 million stolen credit and debit cards, and that the compromised records came from Saks and Lord & Taylor customers."
Source: Associated Press
15. SheIn.com — 6.42 million
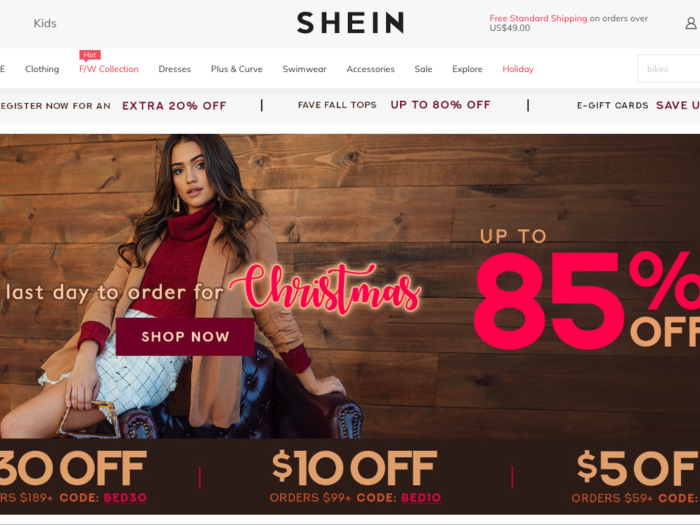
What was affected: Email addresses and encrypted passwords for customers' online store accounts.
When it happened: Sometime in June 2018
How it happened: Hackers carried out "a sophisticated criminal cyberattack on its computer network."
Source: ZDNet
14. Cathay Pacific Airways — 9.4 million

What was affected: 860,000 passport numbers; 245,000 Hong Kong identity card numbers; 403 expired credit card numbers; and 27 credit card numbers without the card verification value (CVV).
When it happened: Activity was discovered in March 2018
How it happened: Passenger data was accessed "without authorization."
Source: Reuters
13. Careem — 14 million

What was affected: Names, email addresses, phone numbers, and trip data.
When it happened: January 14, 2018
How it happened: "Access was gained to a computer system that stored customer and driver account information."
Source: Reuters
12. Timehop — 21 million
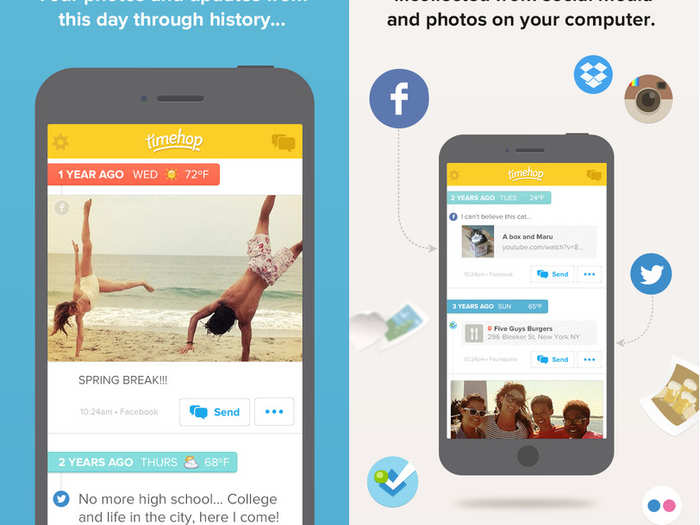
What was affected: Names, email addresses, and some phone numbers.
When it happened: December 2017 — July 2018
How it happened: "An access credential to our cloud computing environment was compromised ... That cloud computing account had not been protected by multifactor authentication."
Source: Business Insider
11. Ticketfly — 27 million

What was affected: Personal information including names, addresses, email addresses, and phone numbers.
When it happened: Late May 2018
How it happened: A hacker called "IsHaKdZ" compromised the site's webmaster and "gained access to a database titled 'backstage,' which contains client information for all the venues, promoters, and festivals that utilize Ticketfly’s services."
Source: The Verge
10. Facebook — 29 million
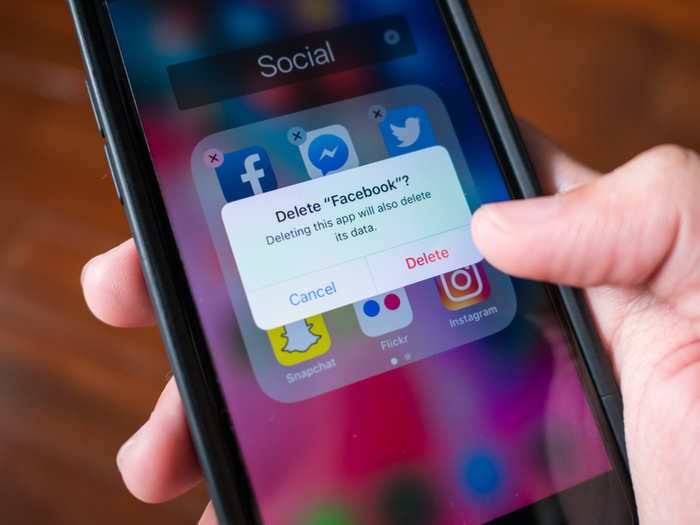
What was affected: Highly sensitive data, including locations, contact details, relationship status, recent searches, and devices used to log in.
When it happened: July 2017 — September 2018
How it happened: "The hackers were able to exploit vulnerabilities in Facebook's code to get their hands on 'access tokens' — essentially digital keys that give them full access to compromised users' accounts — and then scraped users' data."
Source: Business Insider
9. Chegg — 40 million
What was affected: Personal data including names, email addresses, shipping addresses, and account usernames and passwords.
When it happened: April 29, 2018 — September 19, 2018
How it happened: According to Chegg's SEC filing: "An unauthorized party gained access to a Company database that hosts user data for chegg.com and certain of the Company's family of brands such as EasyBib."
Source: ZDNet
8. Google+ — 52.5 million

What was affected: Private information on Google+ profiles, including name, employer and job title, email address, birth date, age, and relationship status.
When it happened: 2015 — March 2018, November 7 — November 13
How it happened: Earlier this year, Google announced it would be shutting down Google+ after a Wall Street Journal report revealed that a software glitch caused Google to expose the personal profile data of 500,000 Google+ users. Then again in December, Google revealed it had experienced a second data breach that affected 52.5 million users. Google has now decided it will shut down Google+ for good in April 2019.
Source: Wall Street Journal, Google
7. Cambridge Analytica — 87 million
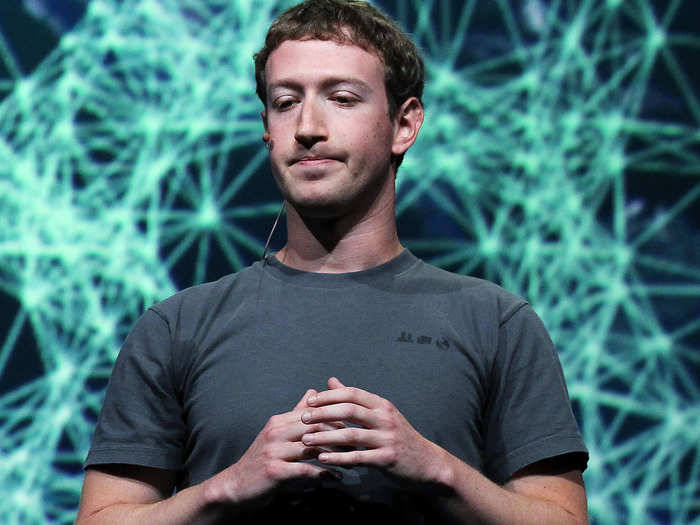
What was affected: Facebook profiles and data identifying users' preferences and interests.
When it happened: 2015
How it happened: An personality prediction app called "thisisyourdigital life," developed by a University of Cambridge professor, improperly passed on user information to third parties that included Cambridge Analytica, a data analytics firm that assisted President Trump's presidential campaign by creating targeted ads using millions of people's voter data.
Only 270,000 Facebook users actually installed the app, but due to Facebook's data sharing policies at the time, the app was able to gather data on millions of their friends.
Source: Business Insider
6. MyHeritage — 92 million
What was affected: Email addresses and encrypted passwords of users who have signed up for the service.
When it happened: October 26, 2017
How it happened: "A trove of email addresses and hashed passwords were sitting on a private server somewhere outside of the company."
Source: Business Insider
5. Quora — 100 million
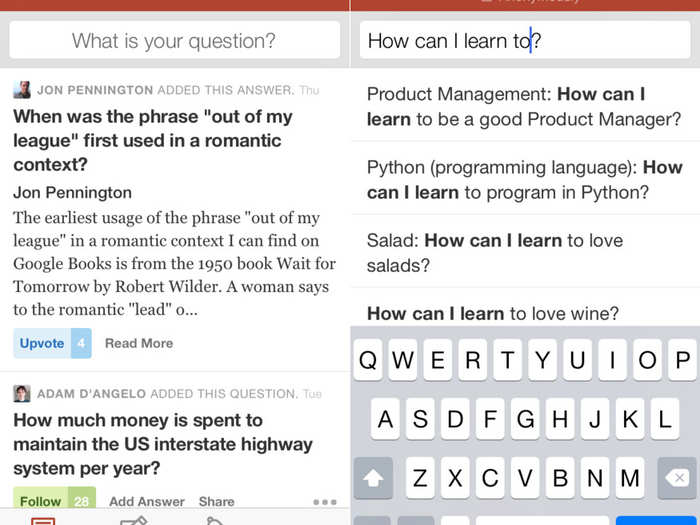
What was affected: Account info including names, email addresses, encrypted passwords, data from user accounts linked to Quora, and users' public questions and answers.
When it happened: Discovered in November 2018
How it happened: A "malicious third party" accessed one of Quora's systems.
Source: Reuters
4. MyFitnessPal — 150 million

What was affected: Usernames, email addresses, and encrypted passwords.
When it happened: February 2018
How it happened: An "unauthorized party" gained access to data from user accounts on MyFitnessPal, an Under Armour-owned fitness app.
Source: Business Insider
3. Exactis — 340 million

What was affected: Detailed information compiled on millions of people and businesses including phone numbers, addresses, personal interests and characteristics, and more.
When it happened: June 2018
How it happened: A security expert spotted a database "with pretty much every US citizen in it" left exposed "on a publicly accessible server," although it's unclear whether any hackers accessed the information.
Source: WIRED
2. Mariott Starwood hotels — 500 million

What was affected: Guest information including phone numbers, email addresses, passport numbers, reservation dates, and some payment card numbers and expiration dates.
When it happened: 2014 — September 2018
How it happened: Hackers accessed the reservation database for Marriott's Starwood hotels, and copied and stole guest information.
Source: Business Insider
1. Aadhar — 1.1 billion

What was affected: Private information on India residents, including names, their 12-digit ID numbers, and information on connected services like bank accounts.
When it happened: It's unclear when the database was first breached, but it was discovered in March 2018.
How it happened: India's government ID database, which stores citizens' identity and biometric info, experienced "a data leak on a system run by a state-owned utility company Indane." Indane hadn't secured their API, which is used to access the database, which gave anyone access to Aadhar information.
Source: ZDNet
Popular Right Now
Advertisement