Representative image BCCL
- Cyberthreats have rapidly been increasing as remote work becomes more prevalent during the COVID-19 pandemic.
- To ensure that employees are being cautious and safe, companies have been sending phishing emails in-house to keep tabs.
- Here are the top ten phishing tricks you should be on the lookout for in your work email, just in case it’s the IT team testing your cybersecurity smarts.
Cyberthreats have grown exponentially as people work from home during the coronavirus pandemic. More IT departments within companies now have the mandate to test the cybersecurity of their employees using phishing tricks.
One tax solution company told Business Insider that their IT team is continuously sending employees fake phishing threats to see if they respond appropriately.
“The crooks are testing you all the time, so you might as well test yourself and get one step ahead,” said Paul Ducklin, the principal research scientist at cybersecurity firm Sophos in a statement.
If you’re working at a big wig company but don’t know if whether the genuine-looking email in your inbox is a phishing threat or not —
Duklin lists out the top 10 most common phishing tricks to watch out for:
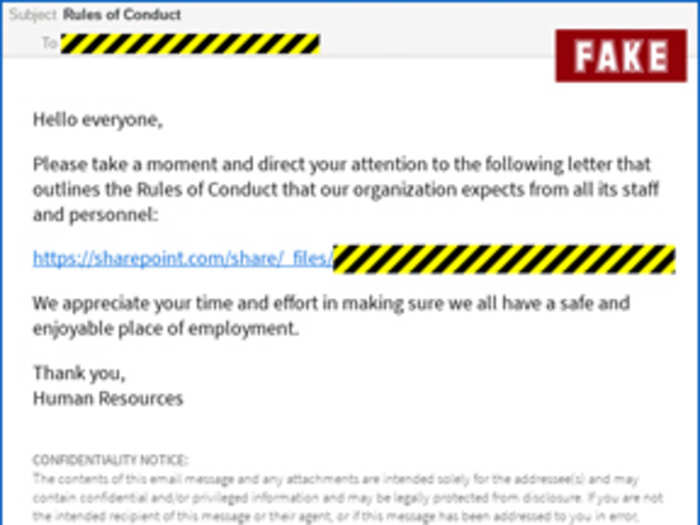
1. Rules of Conduct
Naked security by Sophos
The email looks like a simple enough letter from Human Resources (HR) outlining the company’s new Rules of Conduct. With increasing global diversity at workplaces, concerns over harassment are taken more seriously. And with remote work becoming the new normal, companies are revising their employment and workplace guidelines.
The HR department is mandated to follow up. And because of that, while one must read through the entire guidelines - for many employees - clicking through and approving it feels an easier task. Something that they can get out of the way without having to look into too deeply.
According to Duklin, even if a message looks innocent at first sight, it’s worth a second to look to check for suspicious-looking email addresses, spelling mistakes, or inconsistencies in the terminology.
2. Delayed year-end tax summary
IANS
Clicking on a subject link that addresses tax documentation for work purposes has become a no-questions-asked routine. Most employees simply want to know how long it will be for their forms to come in so that they can file their returns accordingly. It’s one of those ‘necessary evils’ that the world has learned to accept, according to Duklin.
3. Scheduled server maintenance
Pixabay
The research team at Sophos was surprised to see this trick so high up on the list of phishing threats because they assumed that most people are likely to ignore messages from the IT department. However, with more people working from home, the status quo is changing.
Employees want to know when an outage is likely to occur so that they can plan their lives around it.
4. Task assigned to you
Unsplash
The IT department hones down whatever productivity scheduling application is used in house from Slack to Asana, just as genuine threat actors would, so that the email doesn’t obviously stand out as bogus.
5. New email system test
Unsplash
A new way to organise your email or anything to make the daily communication easier is usually welcomed by employees, which makes a new email system test email the easiest way to reel them in.
6. Vacation policy update
Unsplash
First off, who doesn’t want to know if there’s been a change in the way that they can take vacation days? Second of all, the email doesn’t stand out because many companies are genuinely shifting their policies in the wake of remote work and the coronavirus pandemic.
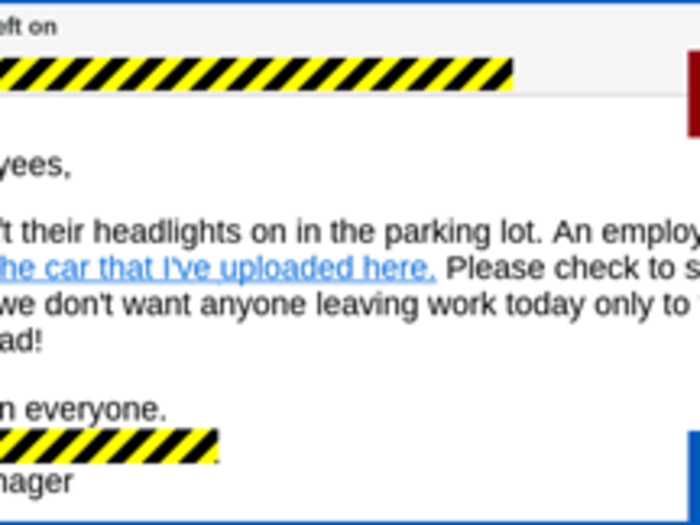
7. Car lights on
Naked security by Sophos
This applies mostly to users in the US who have automated systems to alert them when they’ve left their car lights on.
8. Courier service failed delivery
Unsplash
This trick isn’t specific to the COVID-19 pandemic, but was well-established phishing means even in the old world. Shopping online has become all too common, and if a package isn’t going to get delivered — recipients want to know about it right away.
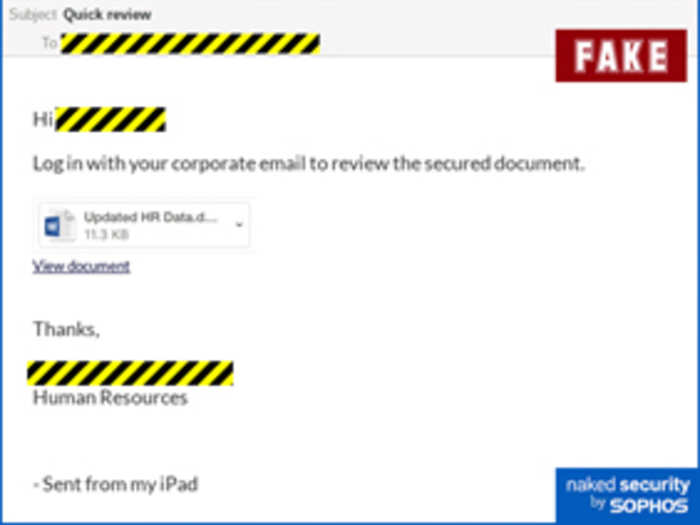
9. Secure document
Naked Security by Sophos
The reason most employees click-through an email is because somewhere, it makes sense that a ‘secured’ document would probably require an extra step or two. The problem is that it can lure employees into submitting their passwords into false platforms or adjust the security setting on their devices.
Before submitting your password anywhere new, it’s best to check in with the IT or whichever is the concerned department first to ensure that it’s not a phishing attempt.
10. Social media message
Unsplash
For employees, this takes the form of a LinkedIn notification since that is the most widely used professional platform. LinkedIn is also enjoying supremacy in the time of COVID-19, with more people on the lookout for new jobs.
In case you do spot a suspicious phishing email in your inbox, reporting it to your company’s security or IT team will, at best, keep your account from getting hacked. And at worst, show your company that you have the cybersecurity smarts.